Risk Meets Real Cybersecurity
The first cyber game
where you actually
hack & conquer.
Real CVEs. Real shells. Real card battles. Breach simulated targets across 196 countries with 300+ security tools — every hack runs in an isolated lab on our servers, never against real systems. Cybersecurity training that actually feels like a game.
For authorized training environments only · All activity is containerized and isolated
Built for security professionals across every discipline
Real Product · No Mockups
See It In Action
Captures from the live platform. Real battles, real conquests, real leaderboards.
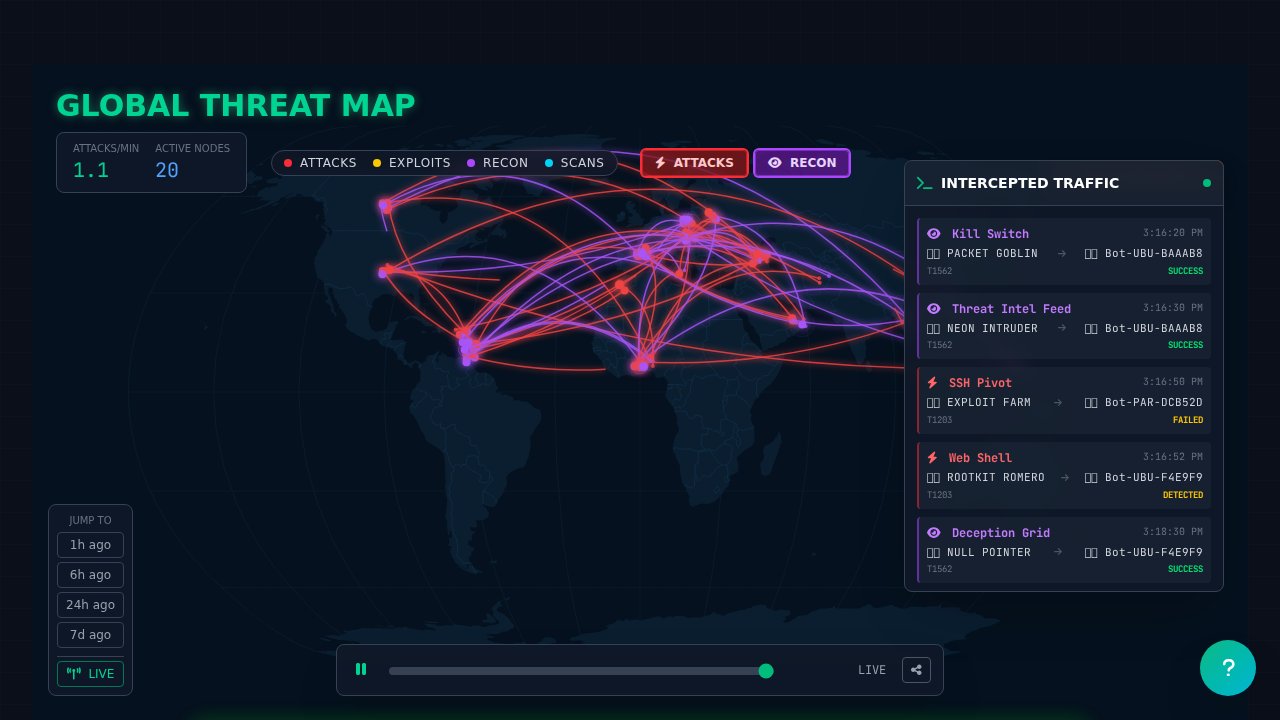
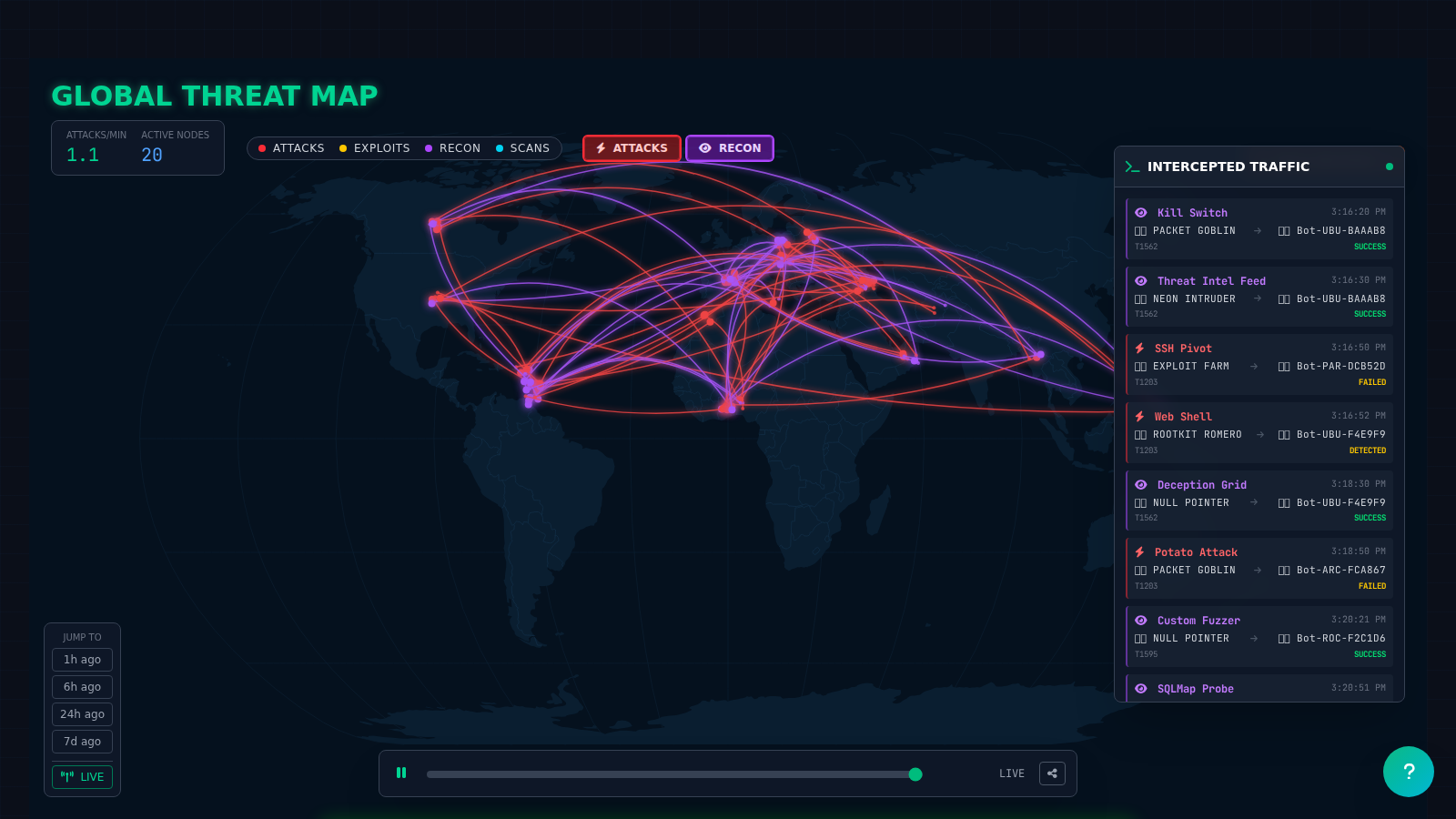
More in-game captures arriving as the closed beta expands — join the waitlist to be among the first to see every system live.
Platform Overview
Adversarial Simulation. End to End.
From node deployment to flag capture — every phase maps to a real-world attack scenario.
Pick Your Target
Choose from Kali, Ubuntu, Windows, Parrot, and Debian targets in isolated sandboxes. Every target carries real CVEs, misconfigurations, and hidden flags — no two missions feel the same.
Execute Real Attacks
Run nmap, Metasploit, SQLMap, Hashcat, Hydra, and 290+ more tools against live services. Every technique tags to a MITRE ATT&CK procedure ID.
Defend & Respond
Configure WAFs, IDS rules, honeypots, and SIEM correlation. Card-based battle mechanics let defenders counter live adversary actions in real time.
Attack Lifecycle
MITRE ATT&CK — End to End
Every tool execution is tagged to a tactic and technique. Track operator progression from initial reconnaissance to full domain compromise.
300+ tools in the arsenal, installable from the store
Live Infrastructure Feed
A World of Targets
Banks, power grids, government endpoints, telecoms, healthcare systems, and military networks across 196 countries — all simulated in isolated game-world environments.
| Target | Category | Status | HP |
|---|---|---|---|
| US_Power_Grid_04 | Energy | CONTESTED | 34% |
| EU_Banking_Cluster_11 | Finance | BREACHED | 8% |
| NATO_Gov_Node_07 | Government | HARDENED | 100% |
| APAC_Telecom_03 | Telecom | SCANNING | 61% |
| UK_Health_DB_02 | Healthcare | CONTESTED | 47% |
Target Categories
What You Get
Platform Capabilities
Everything your security team needs — from beginner CTF labs to expert red team simulations.
Real Targets, Real Exploits
Sandboxed targets running real CVEs and misconfigurations. Your shells, payloads, and privesc attempts hit actual processes — no fake “correct answer” prompts, no simulation layer.
Global Conquest Map
196 countries with subnet assignments, coordinated attack mechanics, country bonuses, and a live Kaspersky-style attack visualization.
Real-Time PvP Battles
Card-based 1v1 and team battles with AI bot opponents. Decks, synergies, archetypes, and countermeasures — skill meets tactical strategy.
300+ Security Tools
nmap, Metasploit, sqlmap, Hydra, Hashcat, Gobuster, Nuclei, and hundreds more. Install via the Store, run directly from the in-browser terminal.
CTF Flag System
Every node hides flags in standard format. Capture, submit, earn points. Compete on per-season leaderboards across 196 country regions.
University & Certs
Structured learning paths aligned to NIST, MITRE, and CompTIA frameworks. Earn certificates. Manage team training with cohort dashboards.
Competition Layer
Card Battle — Skill Meets Strategy
Real-time PvP card combat layered on top of actual offensive security — every play maps to a real attack technique.
Attack Cards
- Network Exploitation
- Social Engineering
- Zero-Day Modules
- Persistent Access
- Data Exfiltration
Defense Cards
- WAF Deployment
- IDS Signature Updates
- Honeypot Traps
- Incident Response
- Patch Automation
AI Opponents
- Adaptive tactics
- Threat actor profiling
- Difficulty tiers
- Strategy simulation
- Team-mode AI
Interested? Join the Waitlist.
NodeBreach is currently in closed beta. We're onboarding security teams, training programs, and individual operators in batches. Register your interest and we'll reach out when access opens.
You're on the list.
We'll notify you when access opens. No further action needed.